As we approach 2026, the digital landscape continues to evolve, yet one relic from the past stubbornly persists in causing security headaches. WinRAR, the compression tool that first launched in 1995, finds itself back in the spotlight for all the wrong reasons. Despite being over 30 years old, this Windows program continues to be a source of security vulnerabilities that keep cybersecurity experts on high alert.
The Latest Security Scare
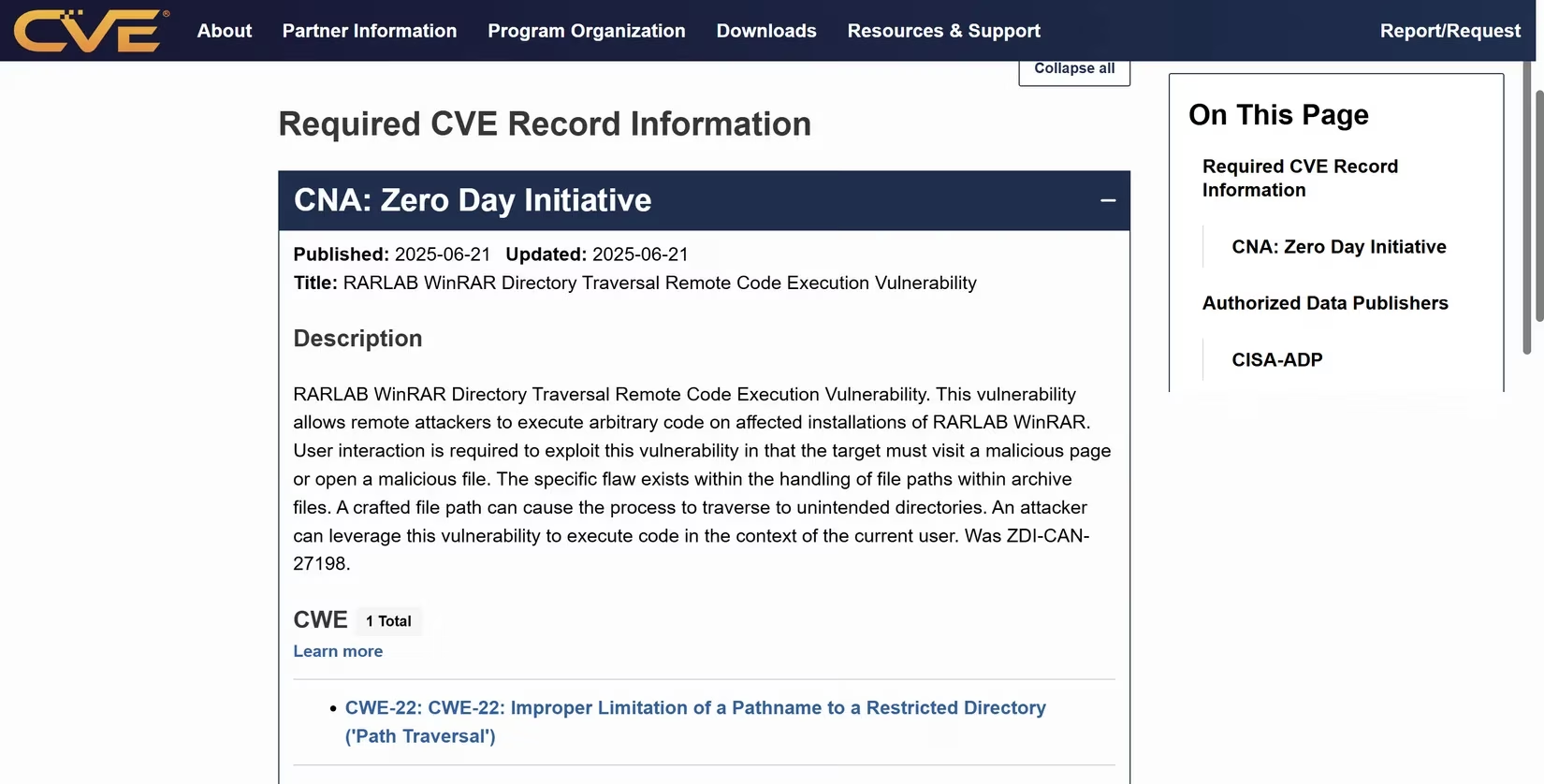
Just before the holiday season in 2025, CISA quietly added two new exploited vulnerabilities to its Known Exploited Vulnerabilities list. Among them was CVE-2025-6218, a directory traversal remote code execution vulnerability affecting WinRAR. This vulnerability allows attackers to execute remote code on systems running vulnerable versions of the software simply by getting users to interact with a malicious file or webpage.
What makes this particularly concerning is that while RARLAB actually patched this vulnerability back in June 2025, many users continue to run outdated versions of the application. Security researchers from multiple firms including BI.ZONE, Foresiet, SecPod, and Synaptic Security have observed active exploitation by at least two distinct threat actor groups.
Why WinRAR Keeps Making Headlines
The program's security track record reads like a cybersecurity horror story. Remember the 2018 incident where a 20-year-old vulnerability was discovered? That exploit allowed attackers to craft archives that extracted files outside their intended folders, leading to millions of successful attacks. The solution back then wasn't a proper patch—WinRAR simply removed support for the vulnerable ACE file format entirely.
The Legacy Code Problem
At the heart of WinRAR's security issues lies its extensive legacy codebase. The software maintains support for numerous archive formats, many of which are practically obsolete in 2025. Each format requires custom parsing code, and each parser represents a potential vulnerability. Much of this code was written decades ago, creating attack surfaces that simply don't exist in modern, minimalist archiving tools.
The User Factor
Let's be real—how many people actually pay for WinRAR? The eternal trial version has become something of an internet meme, but it also means millions of users are running outdated software. Many people install WinRAR out of habit without considering whether they actually need it or if better alternatives exist.
Modern Alternatives Exist
In 2025, there's really no excuse to stick with WinRAR. Modern alternatives like PeaZip offer:
-
Better security track records
-
Faster performance
-
Genuinely free usage (no "eternal trial" nonsense)
-
Support for all relevant archive formats
Even Windows itself has improved its native support for compression formats over the years. The truth is, you don't need WinRAR to handle RAR files anymore—virtually every modern compression tool can manage them without the security baggage.
The Bottom Line
WinRAR's continued presence in the cybersecurity vulnerability reports serves as a reminder that legacy software carries inherent risks. While the developers have attempted to address security issues, the combination of ancient code, support for obsolete formats, and users reluctant to update creates a perfect storm for exploitation.
As we move into 2026, perhaps it's time to finally bid farewell to this digital relic and embrace more secure, modern alternatives that won't keep cybersecurity professionals up at night.
Leave a Comment